The public cloud is becoming more and more popular, and companies are even hosting their most sensitive data and applications there. Public clouds offer different ways to encrypt data while it’s in motion and while it’s at rest.
But what about data that’s being processed or data in use?
The importance of ensuring the safety of data increases when it comes to
- Secure financial data
- Ensure the privacy of patient information.
- Carry out methods of machine learning on private information.
- Apply algorithms to collections of encrypted data originating from a variety of sources.
Use cases and scenarios
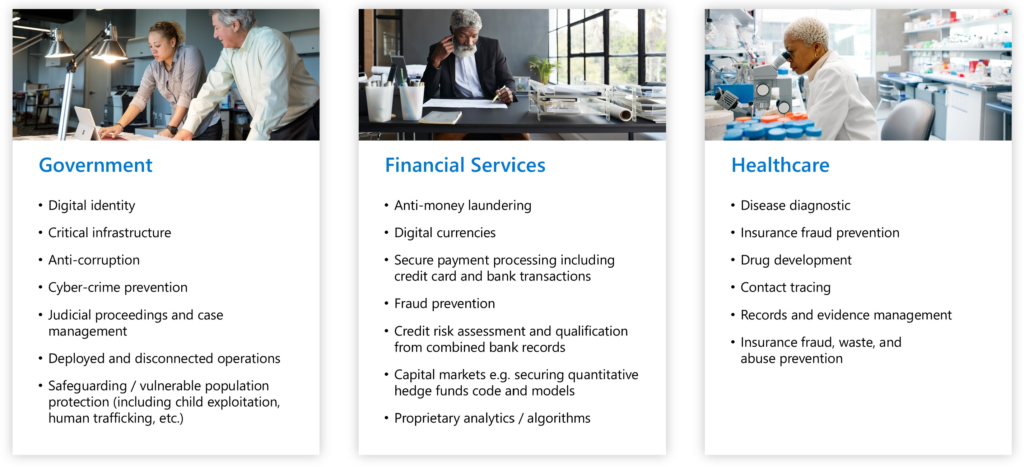
Confidential Computing is applicable to a variety of use cases for the purpose of data protection in regulated businesses such as the government, financial services, and healthcare institutions.
Protecting Data in Use with Microsoft Confidential Computing
Public clouds already have a lot of tools, like client-side encryption and server-side encryption, to protect data while it’s at rest. They also have ways to encrypt data while it is in transit, using secure protocols like TLS and HTTPS. What about data encryption for data in use?
With Recent CPU advancements enabling secret computing implementations include Intel Software Guard Extensions (Intel SGX) and AMD Secure Encrypted Virtualization (SEV-SNP). These technologies are developed as virtualization extensions, and they include feature sets such as memory encryption and integrity, CPU-state confidentiality and integrity, and attestation, which are used to form the confidential computing threat model.
In this post, I’ll talk about how organizations can use the Microsoft Azure Confidential Computing platform to:
- make sure that Microsoft can’t get to unencrypted data?
- ensure company’s security from being harmed by privileged admins?
- guard sensitive customer data stored in the public cloud against access by unauthorized parties?
The confidential computing term established by the Confidential Computing Consortium (CCC) defines confidential computing as: “The protection of data in use by performing computations in a hardware-based Trusted Execution Environment (TEE).”
TEEs are safe environments that keep applications and data from being changed or accessed by people who shouldn’t be able to while they are being used. TEE is the isolated execution environment, or in other words, a secure area of the central processor. TEEs or encryption mechanism implementations remove any outside unauthorized access or voids. With the help of TEE, confidential computing isolates the software and data from the underlying hardware, and the whole operating system is encrypted at the hardware level.
Microsoft Azure Products and Services
Confidential computing is built on making sure that applications are running in a private way. This check is done in several ways and depends on the following suite of Azure services:
- Microsoft Azure Attestation is a remote attestation service that can validate the trustworthiness of numerous Trusted Execution Environments (TEEs) and verify the integrity of the binaries that are operating inside of the TEEs.
- Azure Key Vault Managed HSM is a cloud solution that is completely managed and highly available that allows you to protect cryptographic keys for your cloud applications.
- Trusted Launch includes robust security features such as secure boot, virtual trusted platform module, and boot integrity monitoring, which guard against boot kits, rootkits, and kernel-level malware.
- The Azure Confidential Ledger is a tamper-proof register for storing sensitive data for record keeping and auditing, as well as for data transparency in multi-party settings.
- Azure IoT Edge provides confidential apps that operate inside secure enclaves on Internet of Things (IoT) devices.
- In Azure SQL, data is always encrypted using secure enclaves. The security of sensitive data is safeguarded from viruses and highly privileged unauthorized users by conducting SQL queries directly within a TEE.
Azure Computational Computing leverages these technologies in the following computation resources:
- Confidential VMs with Intel SGX application enclaves. Azure provides the DCsv2, DCsv3, and DCdsv3 series for hardware-based enclave construction based on Intel SGX technology. To safeguard your application data and code in use, you may create secure enclave-based apps that operate in a series of virtual machines.
- App-enclave aware containers operating on Azure Kubernetes Service (AKS). Intel SGX is used by AKS’s confidential computing nodes to construct separated enclave environments in the nodes between each container application.
- Confidential VMs based on AMD SEV-SNP technology make it possible to move existing workloads to the cloud and keep data safe from the cloud operator.
- Confidential Inference ONNX Runtime, a Machine Learning (ML) inference server that restricts the ML hosting party from accessing both the inferencing request and its corresponding response.
Confidential Computing Deployment Models
Azure confidential computing supports multiple deployment models.
- For Infrastructure as a Service (IaaS), it is possible to utilize confidential virtual machines (VMs) for private computing. You may deploy VMs based on –
- Intel Software Guard Extensions (SGX) application enclaves – Intel SGX aids in data protection by isolating applications. To aid strengthen application security, developers may divide their program into hardened enclaves or trusted execution modules by shielding chosen code and data from alteration.
- AMD SEV-SNP technology – AMD SEV-SNP provides hardware-encrypted security for the whole VM against illegal host administrator access.
- Confidential containers in confidential computing may be used for Platform as a Service (PaaS). Enclave-aware containers in Azure Kubernetes Service are included in this offering (AKS).
Hope this will be informative for you, please do share if you find worth sharing it.